Bangalore, May 16 2017: Continuing our coverage of the global wave of Ransomware, we bring you inputs and suggestions from leading enterprises with a stake or expertise in Net security:
Preventive action suggested by e-Scan:
Post infection action suggested by Fortiguard: If your organization has been affected by ransomware, here are some things to do:
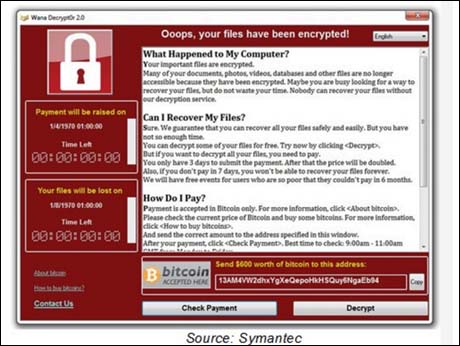
Brad Smith, President and Chief Legal Offic,Microsoft wrote in a blog on May 14: The malicious “WannaCrypt” software quickly spread globally, blocking customers from their data unless they paid a ransom using Bitcoin. The WannaCrypt exploits used in the attack were drawn from the exploits stolen from the National Security Agency, or NSA, in the United States. That theft was publicly reported earlier this year...
This attack provides yet another example of why the stockpiling of vulnerabilities by governments is such a problem. This is an emerging pattern in 2017. We have seen vulnerabilities stored by the CIA show up on WikiLeaks, and now this vulnerability stolen from the NSA has affected customers around the world. Repeatedly, exploits in the hands of governments have leaked into the public domain and caused widespread damage. An equivalent scenario with conventional weapons would be the U.S. military having some of its Tomahawk missiles stolen. And this most recent attack represents a completely unintended but disconcerting link between the two most serious forms of cybersecurity threats in the world today – nation-state action and organized criminal action...... The governments of the world should treat this attack as a wake-up call.
We need governments to consider the damage to civilians that comes from hoarding these vulnerabilities and the use of these exploits.
Other comments:
LC Singh, Founder, Vice Chairman and CEO of Nihilent Technologies The nature of malicious code, or malware, (e.g., viruses, worms, bots) shifted recently from disrupting service to actively seeking financial gain. In the past, worms were designed primarily to propagate. The impact on victims was primarily a disruption of service resulting in loss of productivity and sometimes a loss in revenue. Now, many significant worms are designed to steal sensitive information such as credit card numbers, social security numbers, pin codes, and passwords and send the information to the attacker for nefarious purposes including identity theft. Unfortunately, attackers have become very adept at circumventing traditional defenses such as anti-virus software and firewalls. Standard best practices of deploying latest operating systems, application patches and anti-virus go a long way in reducing these attacks. Organizations must have information security policies that reduce exposure to malware, and will need to develop, deploy, monitor, and test security tools throughout their network. The aim is to detect any hint of anomaly using machine learning on past data, to be able to avoid compromises and, in the event they do get infected, ensure a faster recovery.
Kartik Shahani, Integrated Security Leader, IBM ISA
This ransomware onslaught is a resounding reminder of security basics and hygiene that is required for organizational networks. The incident could have been avoided if critical patches were applied in time throughout companies across all industries. Enterprises constantly struggle to stay on top of regular patching cycles as this can impact day-to-day operations in some cases. IBM has a global incident response and intelligence services (IRIS) team to work with affected clients and those using IBM’s BigFix security patching or QRadar Network protection technologies have been better protected from this attack. IBM’s Managed Security Services team has raised the AlertCon to level 3, which brings a higher level of focus and resources for our clients. We are also leveraging Watson for Cyber Security to analyze the data and derive insights to prevent future incidents. Companies will need to have an incident response plan in place to quickly recover and also ensure that employees, suppliers and others who work with them receives regular security training
Dharminder Nagar MD of Paras Healthcare The recent ransomware attacks that have crippled systems across 99 countries are like a nightmare come true. Unfortunately, given the lackadaisical approach, we often give to cyber security, an attack of this scale was only waiting to happen. While India, as also other Asian nations, have been relatively less hit, we must take this as a serious wake-up call. We are highly underprepared to meet such attacks, with data of millions of people under threat. We cannot prepare to move to a paperless, cashless society until our e-systems are secure. When it comes to healthcare, India’s systems have only recently turned to IT-based procedures. As more and more hospitals digitise their systems, it is highly important for us to take security aspects very seriously.
Ben Gidley, Director of Technology, Irdeto In order to prevent future ransomware security incidents from occurring, organizations must implement policies and procedures to ensure that all PCs are patched properly. Organizations should also implement a defense in depth approach where many layers of security are implemented throughout the company’s IT infrastructure. Currently, most companies focus on protecting their systems from the outside-in with strong perimeter security. But it’s too easy for hackers to get past the perimeter, especially in an open environment which is commonplace for most organizations today. By implementing a defense in depth approach, even if the hacker finds a way to break in, they won’t be able to steal, or hold hostage, what’s inside.
Kiran Deshpande, Co-founder & President of Mojo Networks and President of The Indus Entrepreneurs Association (TiE) Pune, "Simple hygiene of taking regular backups and not opening unknown attachments will have saved users from being affected. However, this is like asking people to eat non-fatty food and do yoga. Not everyone will be upto it. Those in large enterprise will have the services of their IT team and End Point Security and Anti-virus to handle this. Most vulnerable will be the users in small to medium enterprises, startups and professionals like lawyers, doctors, architects who don’t have the cushion of IT services. Nevertheless, one should never pay the ransom as it will encourage attackers. From a security perspective, hackers or bad guys look for weak link to break into. Today, it’s a worm. It can as well be the Wi-Fi environment which unless properly protected can open front door and back door for intrusions to take place. Especially in India, Wi-Fi has been hacked into multiple times to do social damage and create terror. Proper hygiene and overarching security that plugs in multiple holes is the key
ShardaTickoo, Technical Head at Trend Micro, India Primarily the regions that have been attacked by the ransomware ‘WannaCry’ include UK, Europe and the APAC region, which include India as well. The data is still being gathered. It’s more of panic situation been built-up. No specific sectors have been targeted and neither is there an intent to target any specific sector, it’s across Government, IT/ITES, healthcare etc. We have seen customers calling us just to see if the controls are in place. There have been some cases reported, but the number is not significant. Our support lines are jammed, and the team has been working overtime through the weekend. There have been customers who have acknowledged being hit by significant ransomware attacks, and our products at the email gateway solution – advance email security has been able to do a great job of containing it. Customers are under attack but our customers are protected. We have a free online tool for those who aren’t our customer, which can co-exist with their security in place. A customer hotline has been setup, and webinars/workshops have been setup as well.There has already been another variant of the ransomware out yesterday, which does not have a ‘Kill Switch’, making it difficult to contain. The threat actors have upped their ante to ensure the coverage is widespread. As we speak, it has already started infecting countries in UK & Europe, and has not yet spread to India. What is needed is that organizations have a basic hygiene in place, as the modus operandi of these attacks is through phishing emails.
Ram Punamaraju, CEO & CoFounder, Yitsol The ransomware threat is a challenging one for the networks across the globe, spread through emails, the human element responsible for its spread is equally responsible for the treat to grow. The lack of policy framework and lack of understanding of security risks are the major catalysts. Unfortunately, people across the globe have not learnt even after phishing attacks which are very old and most profusely used methods by Cyber criminals as these ransomware attacks are spread in the similar ways