Bangalore, December 27 2016: This is the time of year when technology pundits put on their thinking caps, look into crystal balls, pull out their Tarot cards and do whatever it takes to try and second-guess the trends of the year ahead. For Net security companies this is so often a doom-and-gloom story. With each passing year, as their own preventive solutions are refined, the bad guys are just a megabyte behind trying to penetrate freshly elected firewalls.
Nor do they always concur. Like the Blind Men of Hindustan, all groping the elephant in the famous Victorian-era poem of John Godfrey Saxe and coming to different conclusions, "each in his own opinion, exceeding stiff and strong,...was partly in the right."
We don't claim any special wisdom; so, to provide our readers the most complete picture of the cyber threat scenario in 2017, we compiled the key findings of three leaders. We have already sharedFortinet's predictions. Here is the 2nd:
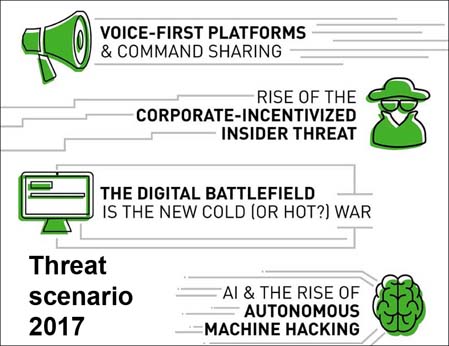
Global cybersecurity leader Forcepoint in its 2017 Cybersecurity Predictions Report. examines the increasing convergence of the technological and the physical worlds and the long term implications of this new digital ecosystem on organizations and institutions worldwide. Some of this year’s predictions: